With millions of websites and different types of sophisticated malware out there, cyber crime is becoming more common than car theft. In this article I’ll show you some different ways to scan WordPress websites for malware.
WordPress sites are a frequent target of spammers, hackers, and malicious software. This is simply because WordPress is the most popular online content management system and its inner workings are well known to hackers. You wouldn’t leave your car key in the ignition, but if you have a site with a dated WordPress version and generic settings, you might as well include tags that say “hacker friendly”.
Every WordPress site owner should take measures toward improving WordPress security.
The standard tactic of most hackers is the easiest – infecting your site with malware. These threats can include:
- Pharma hacks, which inject spam into files or databases
- Drive-by download – scripts that download malicious files to a users computer, generally without their even being aware of it. The download might be masquerading as some useful utility, or covertly bundled with another legitimate program.
- Backdoors – a program that gives hackers access whenever they like, either via FTP uploads or even your WordPress admin dashboard.
- Database or file injection – insertion of code into database or system files that gives hackers access. Database injections are a common threat where text sprinkled through various records can be reassembled by a simple query into malicious commands. WordPress uses a single MySQL database that contains all the settings and information needed to administer your site.
- Redirects – a piece of code that sends visitors from your links to a page on a hacker site that tricks people into downloading malicious files. They might even copy one of your own pages so the user doesn’t even know they’ve been sent to another site.
- Phishing – a fraudulent page/form asking for sensitive information like usernames, passwords, and account numbers which are captured by the hackers and used to access accounts. Often this will be a very good copy of a legitimate site you might deal with, such as a bank or Paypal, which they’ve identified from your web activity. Except that all the information you enter goes straight to a hacker’s personal files.
Defacements
Some hackers aren’t merely content with getting information or even crippling a targeted site; they deface a page (and drive away your customers) by placing a header or image that declares something like “This site has been hacked by the Goon Squad!”
Website defacement is actually rare compared to infection by malware, but it is a favored tactic of some hackers. The majority wish to remain hidden so they can go on with the criminal activity of stealing information and compromising accounts.
When hackers show themselves the first thing you need to do is locate and remove the offending files. But apart from a certain gratification of ego, they get the satisfaction of knowing your site is exposed as hackable to your visitors, which could cost you traffic and do as much damage to your bottom line as if they had actually gotten to your bank account.
WordPress Hackers will bide their time
In most cases, covert hacking means more time for the hacker to operate and more visitors they can potentially scam or infect. A WordPress site might be hacked without the owner ever knowing, meaning that not just you but all your customers are exposed.
Hackers might introduce malware to your site and wait to activate it so any changes that show up on scans seem harmless, since there isn’t a problem. Then they discreetly start to implement malicious scripts to gain further access and control, meaning essentially that they can get whatever they want from your site, whenever they want, if they aren’t discovered.
It is very important to do a regular scan of your website’s files to uncover and malware that might have been introduced. Your site might seem to be operating perfectly fine when in fact it’s been badly compromised. The hacker could already have your IP address, or have copied session cookies that give access to your WordPress dashboard. Some hackers will implement code designed to create the illusion that everything is normal with your system files and everything must be OK. In reality they could already have stolen all the sensitive information they can find and be using your email and user accounts to spam for more victims.
If search engines like Google identify your site as a source of malware, forget about those rankings you worked so hard to get. Not only will you be blacklisted, but your site could show up in browsers with a security warning as a malicious site. Visitors disappear when you were under the impression that things were going well.
Fortunately there are a number of plugins or available 3rd-party services that can help identify malware on a WordPress site. Most ot these site checkers work by typing in your URL, clicking a scan button, and waiting for results. However, these scans may not include hidden or archived files and pages, or recognize the code of particularly innovative hacking attempts. In short, nothing is 100% guaranteed.
WordPress Scanning Tools
Sucuri
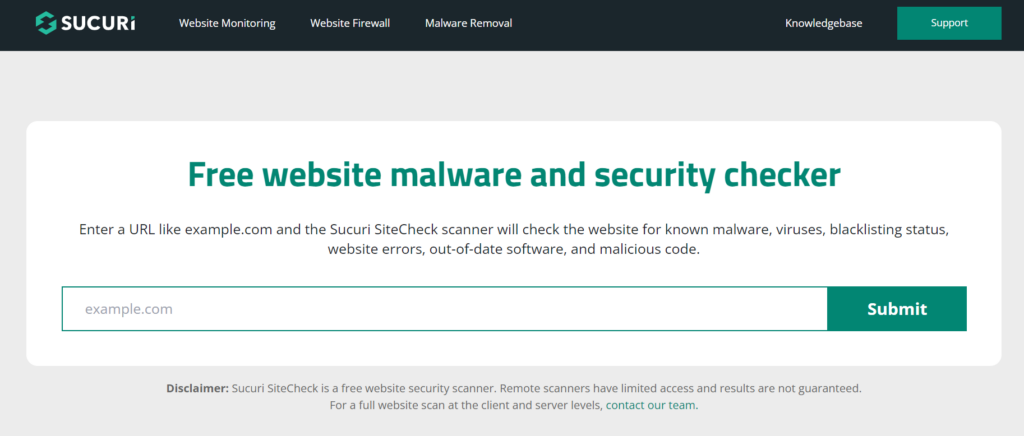
This company has a solid reputation when it comes to security measures and malware scans. SiteCheck by Securi can be used to scan your site for known issues with their free trial version.
SiteCheck malware scanning checks not only for malicious software, but defacements and injection attacks. It can also detect whether compromised email accounts have led to your website server getting blacklisted by spam recipients.
The main drawback to the free version is that you have to scan your site manually on your own, and the results are limited because it is a remote scanner. Upgrading to the paid premium plan offers a much more comprehensive product. It includes automatic alerts via email about any suspicious issues. The full version will remove the malware and remove your IP address from remote server spam lists.
Sucuri also offers a plugin called Sucuri Security that offers firewall protection along with malware scans. It also works to provide additional security to known WordPress vulnerabilities, and provides you with a list of logins so you can see exactly who has been using your site. It also has some useful features for recovering in the event you are hacked, such as a utility for resetting passwords.
Virustotal

This is a free web service that identifies and analyzes suspicious files and associated URLs on your site, helping you to detect viruses, worms, and other kinds of malware.
CodeGuard

This is really a backup program that creates automated file backup and restore operations with a single click. But it also monitors your site regularly for changes and sends alerts if it detects possible malware. In any case every site should be performing regular backups to preserve files and data in the event they are corrupted.
CodeGuard plans are very affordable for basic service. VaultPress performs many of the same services but at a higher fee.
Wordfence Security

One of the more popular WordPress security plugins, it will scan not just theme files, but core WordPress files and other plugins for known threats. It can also deliver a change log to help identify malicious uploads as well as recommendations for making your site more secure.
Wordfence checks against earlier versions saved to your repository. It also has the capability to do scans outside of the WordPress installation, which is a good idea if you have working files in other folders.
There are both free and premium versions of the product, with the latter offering more features and services suitable to businesses of a variety of different sizes and needs.
Hacker Target
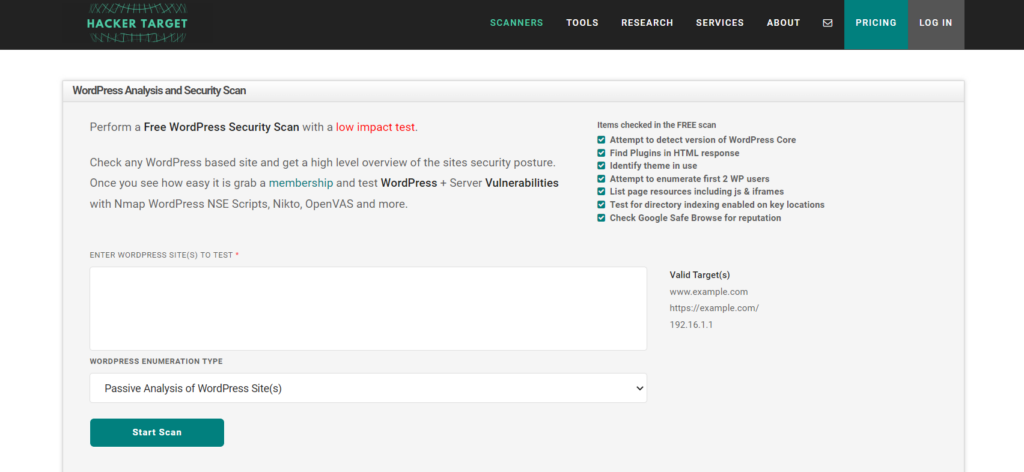
HackerTarget is a powerful online scanning tool that offers a suite of security testing services to identify vulnerabilities and potential security issues in websites. One of the primary features of HackerTarget is its WordPress Security Scan.
The free product conducts a ‘low impact’ scan of the most basic critical areas where malware or corruption may be present. Deeper are more sensitive scans are available in their premium products.
The scanner performs multiple checks, such as identifying outdated plugins, themes, and WordPress core installations that may contain vulnerabilities. By scanning for known security issues and misconfigurations, it helps website owners address potential weaknesses before they can be exploited by cybercriminals.
HackerTarget also checks for issues like directory listing vulnerabilities, which may reveal sensitive information about the website’s structure and resources. It also evaluates header configurations and SSL/TLS certificates. Reporting of any detected issues is really well put together, along with actionable recommendations to fix them.
IsItWP Security Scanner
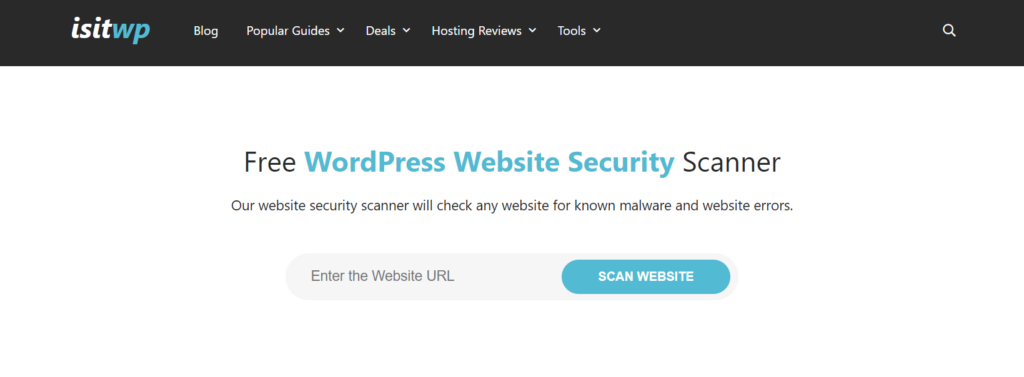
Using IsItWP Security Scanner is simple. All you have to do is type your website address into the tool, and it will start scanning your site. It checks for problems like harmful software, bad links, and other things that can cause trouble for your site.
The best part is that when the scan is done, IsItWP Security Scanner will show you a report with all the problems it found. The report also tells you how to fix those problems so your website can be safe again.
WPSec
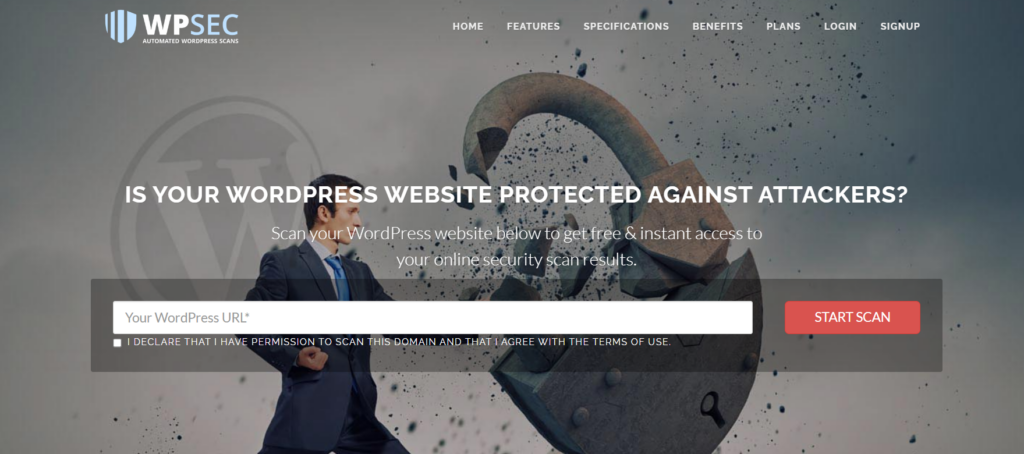
To use WPSec, you simply enter your website’s URL into the scanner. The tool then checks your site for various security issues, such as malware, outdated software, and vulnerabilities that hackers could exploit. It can efficiently assess a WordPress website, providing results in a relatively short amount of time compared to some other scanners.
WPSec has a simple and easy-to-use interface, making it accessible to users with varying levels of technical expertise. The scanner’s straightforward design allows users to quickly initiate a scan and understand the results.
There are free and premium versions of the tool available. Each provides clear, actionable reports with guidance on how to resolve identified issues. The reports are easy to understand and offer valuable insights into enhancing a site’s security.
WordPress Malware Security Plugins
If you have a lot of image files, you might want an option that lets you exclude them from scans, otherwise the process might be slowed considerably.
Theme Authenticity Checker
This plugin tool can scan your WordPress theme files for malicious content, including illicit footer links and Base64 code injection issues. It will return details on any links that are hard-coded into the template, and while this may not be actually malware, it’s worth checking now and then to see that nothing potentially harmful has been passed in.
WP Cerber Security
WP Cerber Security is a powerful security plugin that offers comprehensive protection for your WordPress website. Features include a robust firewall, malware scanner, and anti-spam protection. The plugin also offers IP blocking, login security, and two-factor authentication, ensuring your website is well-protected from cyber threats.
AntiVirus
This is a simply named, free plugin that scans theme files for spam and malicious code. One of its best features is a convenient alert message that shows up right on your WordPress admin bar. Other options regarding malware detection include email alerts. However, AntiVirus only scans your current themes; other installed themes are not scanned. Unless you’re one of those who like changing themes from time to time, unused themes represent an additional level of risk and should be removed.
Anti-Malware
This is another excellent security plugin that scans and automatically removes malware, viruses, and other identified threats from your WordPress site. It can also beef up your wp-login code to prevent any brute-force login attempts.
Quttera
This plugin, named Quttera Web Malware Scanner, scans your site and generates an easy-to-follow report showing possible threats such as backdoors, malicious iframes, code injection, and much more. It also notifies you if your site has been blacklisted for spam by ISPs.
Wemahu
This is a fairly new plugin that will regularly scan your WordPress site for malicious code and email you a report of detected threats.
Security Ninja
Once activated, Security Ninja will scan your website for potential security problems, such as weak passwords, outdated software, and incorrect settings. It also checks for malware on your website and alerts you to any issues, so you can take action to remove it and keep your website safe.
Another useful feature of Security Ninja is the ability to perform automatic scans on a regular basis. This helps you stay proactive in maintaining your website’s security, ensuring that it is always up to date and protected from new threats.
A hands-on approach
A basic technique you should not overlook is manually searching for inconsistencies in the code of your WordPress core files, or sudden changes in file size that could indicate the addition of unusual PHP scripts. A good method is to have recent backup copies of these files that you can use for comparison.
If you are storing and uploading images to cloud services like Dropbox, you might also want to check these files against the original versions. If you haven’t done image optimization or re-sizing, discrepancies should be easy to spot.
Of course, this involves more work and valuable time. For sites with hundreds of files and images, it’s just unrealistic to spend hours checking and comparing files. You could rely on a change tracker and just verify the files that show up as being altered to ensure they haven’t been compromised. Or find a text-comparison tool which will save you time over going through pages of code you may not be all that familiar with. But you will learn a lot about WordPress and PHP.
If you do maintain recent copies, you only need to delete and replace any suspicious changes.
Every WordPress site should be scanned regularly to identify and remove threats as soon as possible. The longer malware is able to lurk and operate, the more damage it can do to your site and your visitors.
Jamie Spencer
Latest posts by Jamie Spencer (see all)
- How To Make Money As A Kid In 2025 – 6 to 16 Years Old - December 9, 2025
- 17 Of The Best Google Adsense Alternatives 2025 - October 13, 2025
- How to Start a Successful Cryptocurrency Website - September 12, 2024

Hey Jamie! Thanks so much for all the awesome roundup of links. Are there any common wordpress files we, as admi/developers could manually check out quickly to look for malicious code? I know that code can be injected in thousands of pages, but sometimes from what I’ve experienced, I’ve found only a few instances in more common places, usually in files such as wp-config.php and functions.php. Are there any others off the top of your head that are generally targeted by hackers?
Hi Heather.
I use a few of these plugins listed here. http://www.hongkiat.com/blog/wordpress-plugins-detect-malicious-codes/
You don’t need to dig around in the code / files to find this stuff. Use a decent plugin and you’ll be fine.
Jamie
I use AIO Security for firewall and advanced security.
No doubt article is very good , but many wp users install free theme and free plugin which is also one of the reason from where they get infected, User need to add tight setting to protect there website , just installing this plugin will not help .
I heard a lot about tool Sucuri. I also visited their blog to attain more information about the plugin. I also discovered some blogs like a blog from template toaster which teach about security of wordpress websites manually and without use of any plugins. Is that security sufficient for a website or plugins are necessary?
Best online tool to check the malicious code ?
I use Sucuri a lot of the time.
What tool is available that scans the actual database for code already injected?